The Safous Zero Trust Access (ZTA) solution emerges as a comprehensive cybersecurity platform, designed to tackle the growing challenges enterprises face in protecting digital assets in an increasingly interconnected and dynamic world. With the rise of remote work, BYOD policies, and sophisticated cyber threats, the demand for robust, flexible security solutions is more critical than ever.
Safous ZTA steps into this evolving landscape with a secure, identity-based access management solution that embodies the principles of the Zero Trust model. It addresses key concerns such as data breaches, unauthorized access, and the complex management of hybrid work environments. Safous ZTA enhances security while also streamlining user experience and administration, offering a solution that balances stringent security requirements with operational efficiency.
CYBERSECURITY TRANSFORMATION
The cybersecurity landscape is witnessing a significant transformation, driven by the adoption of cloud computing, the decentralization of network perimeters, and the increasing sophistication of cyberattacks. The inadequacies of traditional security measures, such as VPNs, are becoming apparent, marked by scalability issues, vulnerability due to the outdated castle-and-moat security model, and a lack of agility in adapting to new technological challenges. Zero Trust solutions, exemplified by the Safous ZTA platform, rise to meet these challenges, providing a scalable, secure, and agile framework that aligns with the needs of contemporary remote work and cloud adoption, thereby ensuring robust protection for modern workforces.
PRODUCT OVERVIEW
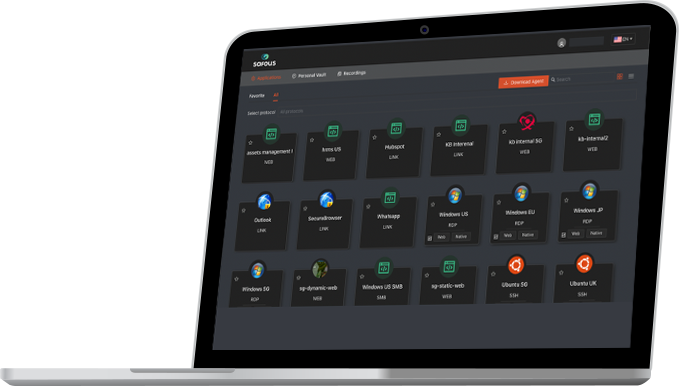
Safous ZTA is an all-in-one platform that offers secure access management across various users, devices, and locations. By leveraging cloud technology, Safous ensures seamless and secure connections to enterprise applications and data. Its suite of features, including Multi-Factor Authentication (MFA), Single Sign-On (SSO), both agentless and agent-based access, and comprehensive audit trails, enables Safous ZTA to accommodate a broad spectrum of use cases, including BYOD, legacy application security, third-party, and inter-company access. What sets Safous apart is its unique blend of adaptability, comprehensive security features, and commitment to data sovereignty, positioning it as a superior choice for enterprises seeking to fortify their defenses with Zero Trust principles.
KEY VALUE AND BENEFITS
Safous ZTA offers a holistic approach to cybersecurity, designed to meet the dynamic requirements of modern enterprises through its versatile and comprehensive security framework.
Key highlights include:
In a rapidly evolving cybersecurity landscape, the CISSP stands out with unique features that set it apart as a top-tier certification. Here are its key differentiators:
• Robust Access Control and Compliance: Safous ZTA champions identity-based access control, adhering to Zero Trust principles to ensure that only authenticated and authorized users gain access to resources. This strict verification approach not only enhances security but also streamlines compliance and operational productivity, making it easier for organizations to manage user access and compliance reporting.
• Adaptable Security for Modern Workforces: Safous’s support for both agentless and agent based access accommodates various devices and environments, including BYOD setups. This flexibility, combined with features like continuous authentication and role-based access control, provides enhanced security for remote and hybrid work models, ensuring adaptability without compromising on security.
• Advanced Security Features: The platform distinguishes itself with comprehensive security features such as advanced data control, session recording, and supervised access. These capabilities not only assist in preventing data leaks and breaches but also in minimizing the organization’s attack surface through application-level access control and Remote Browser Isolation (RBI).
• Scalability and Security Synergy: The inherent flexibility and scalability of Safous ZTA support a wide array of devices and user scenarios, including BYOD policies. This ensures that as organizations grow and evolve, their security measures can adapt accordingly, offering robust protection across the enterprise.
TRUE ZERO TRUST ARCHITECTURE
The Zero Trust model, recognized increasingly as a standard in cybersecurity, addresses the limitations of traditional security perimeters by ensuring access is granted based on stringent authentication, validation, and authorization. Safous ZTA leverages this architecture to enhance remote work security, defend against sophisticated cyber-attacks, and safeguard cloud applications, epitomizing a “True Zero Trust” approach through comprehensive security and compliance features.
1. Data Sovereignty and Security: By not storing any customer data in the Safous cloud and instead keeping it in the customer’s location, Safous upholds the highest standards of data sovereignty and security, aligning with the Zero Trust principle of minimizing exposure and risk.
2. Enhanced Authentication and Access Control: The integration of Multi-Factor Authentication (MFA), device authentication, and Single Sign-On (SSO) across any application or system strengthens user verification processes. This ensures that access is securely managed and granted only to authenticated and authorized users, further embodying the Zero Trust ethos of “never trust, always verify.”
3. Compliance Enablement: Safous’s capability to enable advanced compliance requirements demonstrates its commitment to meeting the stringent regulatory standards that govern data protection and privacy. This aspect is crucial for organizations navigating the complex landscape of global compliance mandates, ensuring they can achieve and maintain compliance through robust security controls.
Together, these elements form the core of Safous’s True Zero Trust model, offering a secure, compliant, and user-friendly solution that protects against modern cyber threats while facilitating seamless access to digital resources. By consolidating various security functions into a single platform, Safous simplifies the management of high-risk access scenarios. This unified approach not only reduces the complexity and potential for security gaps but also enhances the overall security posture with a comprehensive set of tools designed to protect against advanced threats.
ALL-IN-ONE SOLUTION FOR HIGH-RISK ACCESS
Safous’s all-encompassing approach to cybersecurity positions it as a versatile and comprehensive solution for high-risk access, meeting the varied and evolving needs of modern digital enterprises:
• Comprehensive Access Options: The platform’s support for both agentless and agent-based access ensures flexibility and coverage for various user scenarios and device types, making it adaptable to the specific security requirements of IT, IaaS, SaaS, and OT environments.
• Versatile Deployment: With options for cloud and on-premises setup, Safous is designed to seamlessly integrate into any infrastructure, supporting hybrid work models by offering secure access regardless of where users or resources are located.
• Extended Enterprise Security: Safous addresses the challenges of third-party and Bring Your Own Device (BYOD) access by providing secure pathways for external vendors and employees’ personal devices, thereby extending the enterprise security perimeter without compromising the integrity of internal networks.
• Collaboration Across Boundaries: The solution facilitates secure inter-company access, enabling organizations to collaborate more efficiently while maintaining stringent security measures. This capability is essential for businesses that rely on close partnerships and need to share resources securely with other entities.
• Legacy Application Protection: Recognizing the challenges that legacy applications pose to modern security architectures, Safous ensures these applications are securely accessible. This protection is vital for organizations relying on older systems that may not natively support contemporary security protocols.
ADVANCED AI AND OT THREAT DEFENSE
Additionally, Safous ZTA demonstrates its forward-thinking approach by addressing emerging threats from advanced AI and the unique security challenges of operational technology (OT) environments:
• Safous addresses the increasing risks from supply chain attacks and third-party breaches through its secure access capabilities.
• The platform provides secure pathways for external vendors, suppliers, and partners to access enterprise resources without compromising internal networks.
• Stringent access controls, auditing, and monitoring ensure visibility into third-party interactions, mitigating potential supply chain vulnerabilities.
• Safous enables secure inter-company collaboration while maintaining robust security postures across organizational boundaries.
ADAPTING SECURITY TO COMBAT AI-BASED THREATS
By adhering to the core principle of “never trust, always verify.” Safous ensures continuous monitoring and evaluation of all network interactions, regardless of origin, thereby enabling the early detection of abnormal behavior or access patterns through AI and machine learning algorithms. By implementing strict access controls, minimizing privilege levels, and enforcing micro-segmentation, Zero Trust significantly reduces the attack surface, making it harder for AI-driven attacks to proliferate or move laterally across the network. Furthermore, enhanced authentication methods, including multi-factor authentication and behavioral analysis, strengthen defenses against sophisticated AI threats. This proactive and comprehensive security posture ensures that even the most advanced AI threats are identified and mitigated promptly, safeguarding critical data and systems effectively within a Zero Trust environment.
ROBUST OT AND REMOTE PRIVILEGED ACCESS MANAGEMENT (RPAM)
Safous provides comprehensive Remote Privileged Access Management (RPAM) capabilities, securing remote privileged access for both IT and Operational Technology (OT) environments.
Its advanced authentication, access controls, and oversight functionalities make it well-suited for securing critical OT systems and cyber-physical systems (CPS). By replacing or augmenting traditional remote access tools, Safous enhances security for organizations operating CPS, where cyber threats can have catastrophic consequences. The platform streamlines secure remote access for third-party vendors and contractors, a crucial requirement for industrial enterprises relying on external support.
COMPREHENSIVE ANTI-DATA-LEAKAGE FEATURES
Safous’s robust security architecture is fortified by comprehensive anti-data-leakage features, integrating flexible access and data control mechanisms to prevent unauthorized disclosure and maintian the integrity of critical data:
• Privileged Access Management: By tightly controlling privileged accounts, Safous minimizes the risk of security breaches that could lead to data leakage, ensuring only authorized users haveaccess to critical systems and data.
• MFA/SSO and Integration with Identity Providers (IdPs): Multi-Factor Authentication (MFA) and Single Sign-On (SSO) capabilities ensure a robust authentication process. MFA enhances security by requiring multiple forms of verification from users, while SSO simplifies the user experience by allowing a single set of credentials to access multiple applications. Integration with Identity Providers (IdPs), including local IdP, LDAP/MS Active Directory, and any SAML/OpenID IDaaS (such as AzureAD, Okta, etc.), facilitates seamless identity management and provisioning.
• Audit Trail: Maintaining a detailed record of all system and user activities, Safous’s audit trails enhance visibility and accountability, allowing for the quick identification and response to potential security incidents that could result in data leakage. Safous also enables the close monitoring of users considered to be of low trust, ensuring that their actions do not compromise data security and are in compliance with organizational policies.
• Recording of Critical Sessions: By capturing video recordings of critical sessions, Safous provides an additional layer of security and oversight, allowing organizations to review and analyze user actions retrospectively for signs of mishandling or unauthorized data access.
• Web Browsing Isolation: Safous’s browser isolation feature prevents data leakage by isolating the browsing session from the end user’s device, thereby ensuring that any malicious content encountered online does not reach the corporate network or endpoints.
EASY IMPLEMENTATION
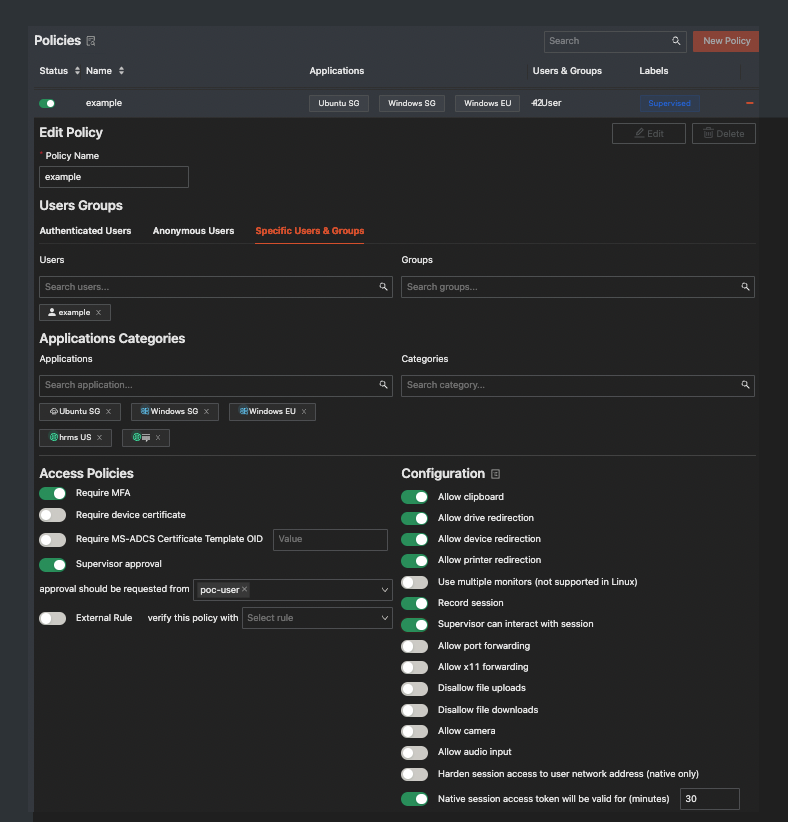
Implementing Safous Zero Trust Access is straightforward and hassle-free, involving a simple two-step process that begins with the installation of the App Gateway. This gateway acts as a centralized control hub for managing critical functions like user authentication and application access. Following this, configuring your policies is made easy through the Safous portal, requiring no additional software. The solution is browser-based and agentless, making it not only easy to deploy but also to scale according to your organization’s needs, emphasizing its user-friendly approach to robust cybersecurity.
CONCLUSION
Safous Zero Trust Access emerges as a holistic and future-proof cybersecurity solution tailored to the evolving needs of modern enterprises. By upholding true Zero Trust principles, implementing robust anti-data leakage mechanisms, and offering advanced capabilities to protect against unauthorized access attacks often stemming from leaked accounts via phishing attacks. Safous ZTA indirectly shields against some of these emerging, and Safous positions itself as an indispensable partner in fortifying digital defences. It proactively addresses the growing risks from supply chain attacks and third-party breaches through its secure access capabilities for the extended enterprise. By fortifying the security perimeter and fostering secure collaboration, Safous enables organizations to confidently embrace partnerships and third-party integrations while safeguarding against potential supply chain vulnerabilities. As technology landscapes transform, Safous remains committed to continuous innovation, ensuring its platform remains resilient and adaptive in the face of emerging cybersecurity challenges.